Welcome to this week's Terraform Weekly newsletter.
Not a log of notable releases this week, but a few good overview articles about pipelines, testing and importing. Things we all care about.
----
A note on the theme here: Terraform is a powerful way to do infrastructure as code — the declarative approach, plan-based workflow and support for many providers makes for productive stack. But, you only get value once you make it over the hump of defining your infrastructure with code, implementing workflows that work, and investing in quality, security, and leverage. This takes a lot of work and can take a long time before the investments pay off.
----
As always, if you have something to include in this newsletter, please email me and if you are interested in sponsoring or partnering, reach out as well.
Shifting Cloud Security Left — Scanning Infrastructure as Code for Security Issues — blog.christophetd.fr
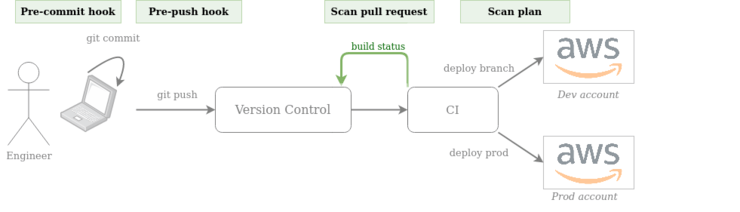
"Shifting left" moving some capability earlier in a development process. Imagine something like a scrum board where work items move from the left to the right.
When you treat infrastructure like all other software (code, code reviews, testing, pipelines), you also shift these things around.
In this article, Christophe Tafani-Dereeper covers many options for statically analyzing terraform code for security issues.
Note- they use a somewhat different definition for static analysis than I would. Normally I refer to a tool as static analysis only if it can run without running the code you are analyzing. Some of the included tools here inspect plan files, which you can only get if you, uh, run the code. I will let this slide.
Anyway, if you are looking at tools for analyzing your terraform for security issues, this guide will help. Send it to your manager too.

Flatiron Health has been using terraform since 2019, initially using Jenkins to automate applies, presumably with developers also running plans from their machines.
They ran into a number of limitations with this approach -
managing terraform versions was hard - they needed the Jenkins server and everyone's workstation to have the same version installed. This meant that terraform upgrades needed to be coordinated across the organization.
Due to compliance requirements, every infrastructure pull request needed to be scrutinized by their security team.
New pipelines were tedious to set up.
They looked at these challenges, evaluated building vs. buying and settled on paying for Terraform Enterprise.
Now they can rely on TFE for version management, use Sentinel for security policy and use the TFE provider to set up new workspaces. Plus cost estimation and SAML integration for single sign-on.
Sounds like a big win for their team.
I have never been a big fan of Cucumber for testing. Maybe just haven't worked on a team that needed it or set things up well.
Clarity is a tool for for using the Cucumber language to test terraform code. I wraps godog, a cucumber implementation in Go.

Infrastructure-as-code is great...if you have have your infrastructure already defined in code.
Migrating pre-existing infrastructure into IaC is toilsome and error-prone.
Thankfully this process is getting better. Terraform has been able to import state for a long time. There are tools like terraformer, which help, but you can also script it yourself.
RJ Zaworski from Koan writes about their approach-
Create a stub definition in Terraform
Import the resource
Replace the stub with the imported state
Cleverly, for step 3, they used `terraform state show` and sed to update the files. I like it.
Notable Releases
Note– Lots of breaking changes. Check the changelog for details. The changes are:
removal of terraform 0.11 support
removal of deprecated workspace ids (they used to use the pretty name for the id, now the ws-$RAND ids are used)
Second alpha for Terraform 0.15 is out.
I have heard from those who would know about this that 0.15 will be the last release before 1.0 (unless it become 1.0 itself).
Also a large number of breaking changes here, again all things that have been deprecated for awhile. The team is clearly in cleanup mode.
Finally...
Thanks for reading, and reading to the end.
If you have something to include in this newsletter, please email me.
If you are interested in sponsoring or partnering, reach out as well.
